1.2.2 "A Flaw in the System's Design..."
Summary
TLDRThis video script discusses the concept of logical vulnerabilities in system design, exemplified by a secure login system. It illustrates how an input flaw, such as using a single quotation mark, can alter code semantics and lead to a code injection attack. The script highlights the simplicity yet elegance of such vulnerabilities, which are prevalent in many websites, as noted by the Open Web Application Security Project (OWASP), ranking it among the top 10 security risks.
Takeaways
- 🔒 A flaw in system design is often referred to as a logical vulnerability.
- 💡 Logical vulnerabilities typically arise from unconsidered usage scenarios.
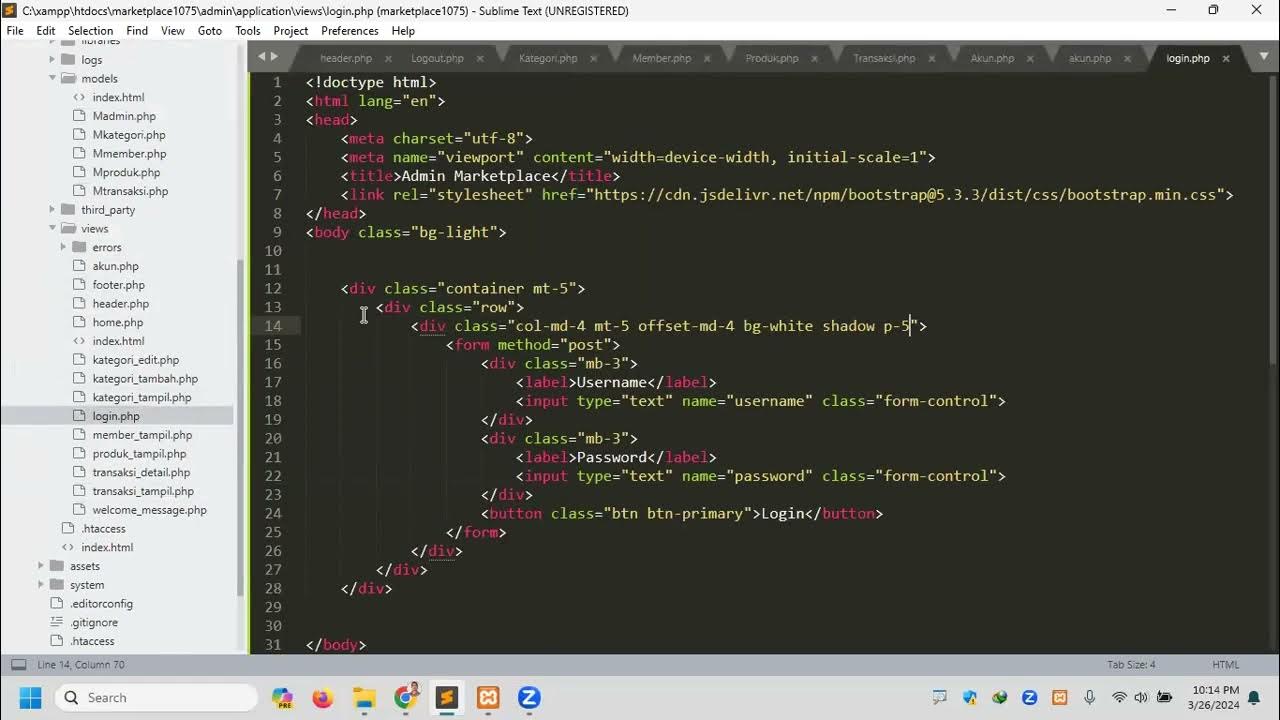
- 👤 An example given is a secure login system that checks for matching username and password records.
- 🐞 Introducing a single quotation mark can alter the code's semantics, leading to unintended behavior.
- 💧 The example demonstrates how a user input can be treated as part of an expression, bypassing security checks.
- 🚨 A code injection attack occurs when user input is executed as code without proper validation.
- 🔑 The script highlights the importance of considering all possible user inputs during system design.
- 📈 According to OWASP, code injection is one of the top 10 security risks.
- 🌐 There are over 300,000 vulnerable websites due to this type of vulnerability.
- 🔍 Understanding such vulnerabilities can potentially allow hacking into numerous systems by exploiting overlooked loopholes.
Q & A
What is a logical vulnerability in the context of system design?
-A logical vulnerability is a flaw in a system's design that arises from an unconsidered usage scenario, often leading to unintended behavior or security breaches.
How does the example of a secure login system demonstrate a logical vulnerability?
-The secure login system example shows a logical vulnerability by illustrating how a user can manipulate the input to bypass authentication, exploiting the system's failure to handle unexpected input correctly.
What is the significance of the single quotation mark in the login example?
-In the login example, the single quotation mark is significant because it alters the syntax of the input string, effectively ending the string prematurely and allowing the rest of the input to be treated as a code expression.
Why does the input 'one equals equals one' lead to a successful login in the example?
-The input 'one equals equals one' leads to a successful login because the expression '1=1' is always true, and since everything after the slashes is ignored as a comment, the system incorrectly authenticates the user.
What type of attack is demonstrated in the video script?
-The attack demonstrated in the video script is a code injection attack, where user input is treated as executable code, leading to unauthorized access or actions.
What is the role of the open web application security project (OWASP) in identifying security risks?
-OWASP plays a role in identifying security risks by providing a list of top security risks, including code injection, and offering guidelines and tools to help developers and organizations protect their web applications.
How does the video script suggest that understanding logical vulnerabilities can lead to hacking?
-The video script suggests that understanding logical vulnerabilities can lead to hacking by highlighting how simple oversights in system design can be exploited to gain unauthorized access to systems, potentially affecting hundreds of thousands of websites.
What is the importance of considering all possible user inputs during system design?
-Considering all possible user inputs during system design is crucial to prevent security vulnerabilities, such as code injection, and ensure that the system behaves as intended under all circumstances.
How can developers mitigate the risk of code injection attacks?
-Developers can mitigate the risk of code injection attacks by implementing input validation, using parameterized queries, and employing secure coding practices to sanitize and escape user inputs.
What is the broader implication of the discussed vulnerability for web application security?
-The broader implication of the discussed vulnerability is that web applications must be designed with comprehensive security measures to handle unexpected or malicious inputs, reinforcing the importance of secure coding and regular security assessments.
Outlines

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードMindmap

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードKeywords

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードHighlights

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードTranscripts

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレード5.0 / 5 (0 votes)