AlgoSec Platform - Full Demo
Summary
TLDRYitzi Tenenbaum introduces AlgoSec's security management solution, emphasizing its business-driven approach to automate network security policy management across cloud, SDN, and enterprise networks. The demonstration showcases key features like application visibility, risk analysis, compliance assurance, and change automation, highlighting how AlgoSec simplifies security policy management, reduces risk, and ensures continuous compliance with minimal manual intervention.
Takeaways
- 🔒 Algosec provides a business-driven approach to security policy management, aligning security with business processes.
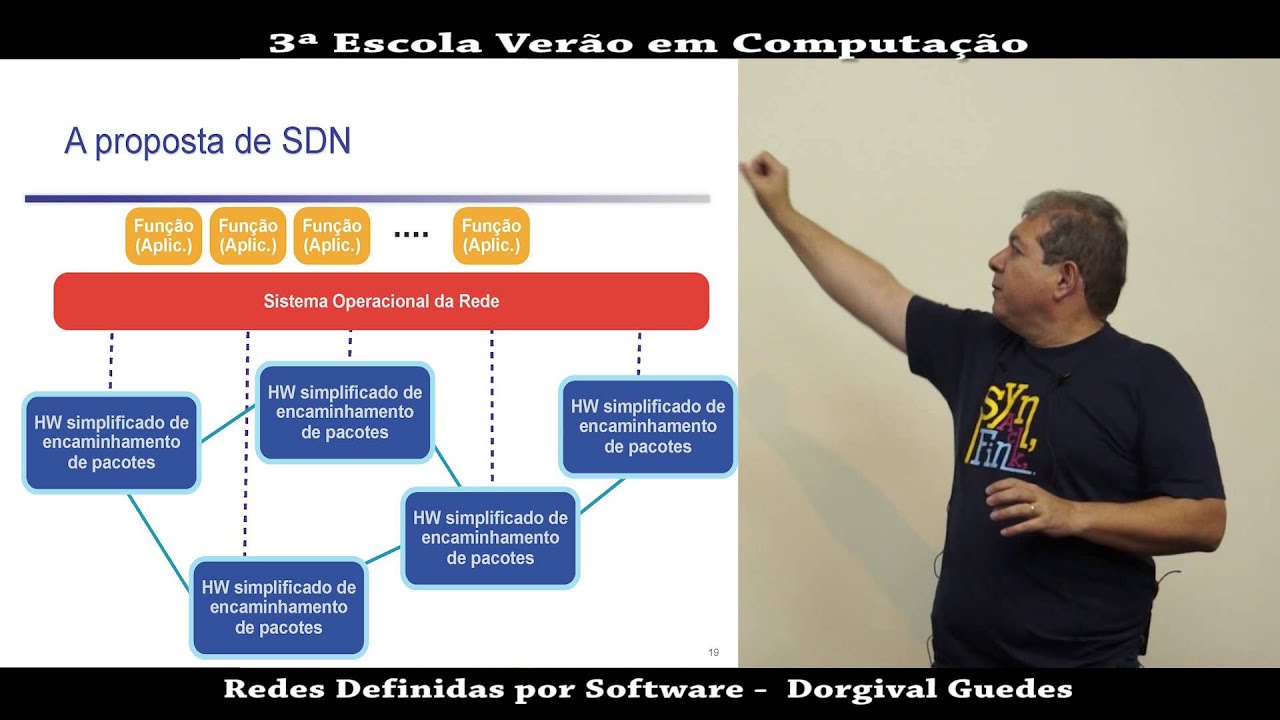
- 🤖 The solution automates and orchestrates network security policy management across cloud, SDN, and on-premise networks.
- 🌐 Key features include automatic discovery of application connectivity requirements, visibility across the entire network, and proactive risk analysis.
- 🔍 AppViz offers application visibility, allowing owners and architects to track connectivity status and vulnerability of business applications.
- 🛡️ Algosec integrates with leading vulnerability management tools to provide application context and visibility into risks.
- 🌟 The solution supports zero-touch automation for security changes, enhancing efficiency and reducing manual intervention.
- 🚦 The automated workflow includes risk checks, policy implementation, and smart validation to ensure secure and efficient changes.
- 🛠️ Fireflow is the orchestration tool within Algosec, facilitating intelligent automation and integration with third-party ticketing solutions.
- 📊 Firewall Analyzer offers reporting, analytics, and infrastructure fundamentals, including risk analysis, policy optimization, and regulatory compliance.
- 🔧 The platform supports comprehensive policy management, including optimization, cleanup, and auditing, across diverse network environments.
Q & A
What is AlgoSec's approach to security policy management?
-AlgoSec's approach to security policy management is business-driven, enabling organizations to automatically manage security based on business applications that power their business.
How does AlgoSec's solution automate network security policy management?
-AlgoSec's solution intelligently automates and orchestrates network security policy management across cloud, SDN, and on-premise enterprise networks.
What is AppVids and how does it provide application visibility?
-AppVids is a component of AlgoSec's solution that provides application visibility into an organization's business applications, geared towards application owners and architects, and helps bridge the communication gap between business and IT.
How does AlgoSec help in discovering application connectivity requirements?
-AlgoSec can automatically discover application connectivity requirements by analyzing network traffic data, which can be collected in multiple ways including NetFlow, sFlow, offline client-based sensors, or live packet forwarding.
What is the purpose of the AlgoSec's auto-discovery feature?
-Auto-discovery enables customers to map their organization's business applications and connectivity flows by analyzing network traffic data, simplifying the process of understanding and managing network security policies.
How does AlgoSec assist in managing security changes with zero touch automation?
-AlgoSec's solution automates time-consuming security changes and enhances them with business-relevant context, allowing for zero-touch automation of policy changes across multiple devices without causing outages.
What is the role of FireFlow in AlgoSec's suite of tools?
-FireFlow is the operational glue that ties AlgoSec's suite together, providing end-to-end intelligent orchestration and automation for network security policy management.
How does AlgoSec help in ensuring continuous compliance?
-AlgoSec's solution ensures continuous compliance by automatically pushing changes directly onto devices, automating time-consuming security changes, and providing visibility and management of network security across the entire enterprise network.
What kind of reports does AlgoSec Firewall Analyzer provide?
-AlgoSec Firewall Analyzer provides a wide variety of powerful, actionable reports including risk analysis, policy optimization, troubleshooting, regulatory compliance, and more.
How does AlgoSec's solution support application portability and cloud migrations?
-AlgoSec's solution supports application portability by enabling faster migrations to public or private clouds and micro-segmentation, providing visibility and management of application connectivity flows independent of underlying security policies.
What is the significance of AlgoSec's traffic simulation accuracy?
-AlgoSec's traffic simulation accuracy is significant as it provides a high level of proficiency in the security policy management space, supported by experience in the world's largest networks and a wide range of routing implementations.
Outlines

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantMindmap

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantKeywords

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantHighlights

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantTranscripts

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantVoir Plus de Vidéos Connexes
5.0 / 5 (0 votes)