An Illustrated Guide to OAuth and OpenID Connect
Summary
TLDRThis video script simplifies the complexities of OAuth and OpenID Connect, two crucial standards for secure data sharing between applications. It explains OAuth 2.0 as a security protocol that allows apps to access user data without passwords, using a key-based authorization process. The script then introduces OpenID Connect as an extension of OAuth, adding user authentication and identity information to the data access capabilities. Through an engaging example of a pun-sharing website, it illustrates the OAuth flow, terminology, and the benefits of using these standards for both users and developers.
Takeaways
- 🔐 OAuth 2.0 is a security standard that allows one application to access data in another application without sharing your username and password.
- 📜 The OAuth flow includes steps for granting permission or consent, often referred to as authorization or delegated authorization.
- 👤 The key roles in OAuth are the resource owner (you), the client (the application requesting access), the authorization server (where you have an account), and the resource server (the service you want to use).
- 🔄 The authorization code flow is the most common OAuth 2.0 flow, involving a series of steps to securely exchange information between services.
- 🔑 The authorization server issues a temporary authorization code, which the client exchanges for an access token to access the resource server on your behalf.
- 🏷️ Scopes define the specific permissions the client is requesting, such as access to data or the ability to perform certain actions.
- 🔗 OpenID Connect (OIDC) is a layer on top of OAuth 2.0 that adds functionality for authentication and providing profile information about the logged-in person.
- 🎟️ With OIDC, the client receives both an access token and an ID token, with the latter containing claims about the user's identity.
- 🔄 The OIDC flow is similar to OAuth, but with the use of a specific scope and the issuance of an ID token, which includes identity information.
- 🌐 OIDC enables single sign-on (SSO) scenarios, allowing users to log in once and access multiple applications with the same credentials.
Q & A
What is the primary issue with sharing your username and password with other services?
-Sharing your username and password with other services is problematic because there's no guarantee that the organization will keep your credentials safe or that their service won't access more of your personal information than necessary.
What is OAuth 2.0 and how does it improve upon the old method of sharing credentials?
-OAuth 2.0 is a security standard that allows one application to access your data in another application without sharing your username and password. Instead, you give one app a key that grants specific permissions to access your data or perform actions on your behalf.
Can you explain the authorization code flow in OAuth 2.0?
-The authorization code flow is a common OAuth 2.0 flow where the client redirects the user to the authorization server, which then asks for permission. If granted, the authorization server sends a temporary authorization code back to the client, which it exchanges for an access token to access the user's data.
What is the role of the 'resource owner' in OAuth 2.0?
-The resource owner is the entity that owns the identity, data, and any actions that can be performed with their account. In the context of the script, the resource owner is the user who grants or denies access to their data to the client application.
What is the difference between an authorization server and a resource server?
-The authorization server is the service that authenticates the resource owner and issues access tokens to the client. The resource server is the service that holds the protected resources and uses the access token to verify that the client is allowed to access the resource.
What is the purpose of a redirect URI in OAuth 2.0?
-The redirect URI is the endpoint to which the authorization server redirects the resource owner back after they have granted or denied permission. This URI is provided by the client and is used to return the authorization code or access token.
How does OpenID Connect extend the functionality of OAuth 2.0?
-OpenID Connect is a layer that sits on top of OAuth 2.0 and adds functionality for authentication and providing basic profile information about the person who is logged in. It allows clients to verify the identity of the resource owner and obtain information like their name and email address.
What is the significance of the ID token in OpenID Connect?
-The ID token in OpenID Connect is a specially formatted string (JSON Web Token or JWT) that contains claims about the resource owner, such as their ID, name, and authentication information. It provides both authorization and identity information to the client.
What is the concept of Single Sign-On (SSO) and how does OpenID Connect support it?
-Single Sign-On (SSO) is a concept where a user logs in once and gains access to multiple applications without needing to log in again. OpenID Connect supports SSO by allowing clients to establish a login session and gain information about the logged-in user across different applications.
How does the OAuth 2.0 flow differ from the OpenID Connect flow?
-The OAuth 2.0 flow focuses on authorization and accessing data, while the OpenID Connect flow includes the same authorization steps but also provides an ID token with identity information. The key difference is that OIDC uses a specific scope in the initial request to indicate that it will return an ID token along with the access token.
Outlines

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantMindmap

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantKeywords

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantHighlights

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantTranscripts

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantVoir Plus de Vidéos Connexes
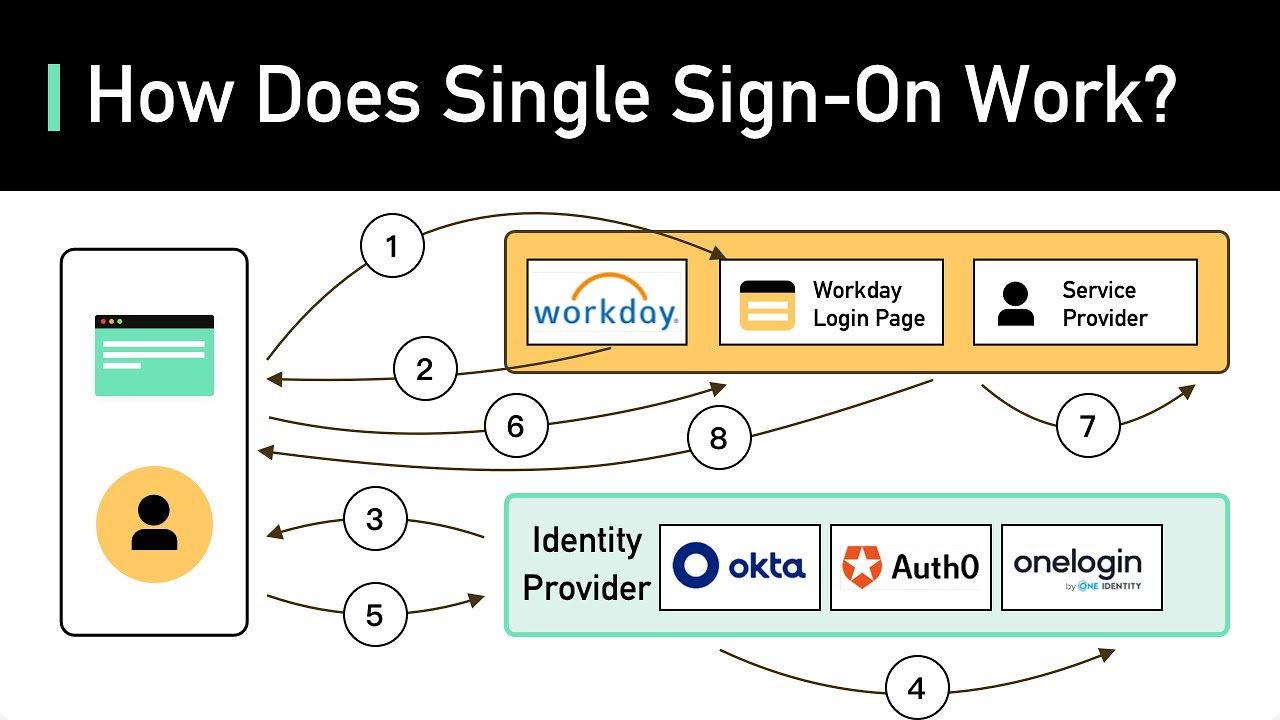
What Is Single Sign-on (SSO)? How It Works
Oauth2 JWT Interview Questions and Answers | Grant types, Scope, Access Token, Claims | Code Decode

7 Authentication Concepts Every Developer Should Know
API Authentication with OAuth using Azure AD
Single Sign On Menggunakan OAuth

SAML vs. OpenID (OIDC): What's the Difference?
5.0 / 5 (0 votes)
