STOP Using Proton & Signal? Here’s the TRUTH
Summary
TLDRThe video discusses recent claims questioning the security of Proton and Signal, highlighting the importance of understanding legal frameworks and operational security. It clarifies that while companies must comply with legal requests, end-to-end encryption protects user data. The video emphasizes the need for users to take personal responsibility for their privacy by using tools like VPNs and being cautious with shared information.
Takeaways
- 🔒 Proton and Signal, once considered secure platforms, are now under scrutiny due to recent events and media coverage.
- 📜 Proton complied with a legal request from Spanish authorities, highlighting the legal obligations companies have to comply with government requests.
- 🔗 The importance of understanding that companies can only provide data they possess, and end-to-end encryption limits what can be handed over.
- 📧 Email and recovery email addresses are inherently not encrypted to ensure delivery, which is a necessary compromise for functionality.
- 🏛️ Companies like Proton must operate within the legal frameworks of their host countries, even if they prioritize user privacy.
- 🧐 The founder of Telegram questioned Signal's encryption, suggesting potential bias and a need for concrete evidence to support such claims.
- 💼 Concerns about Signal's board chairman's history and connections, though the open-source nature of Signal's code provides some reassurance.
- 🛡️ The strength of privacy apps and services depends on the user's operational security (OPSEC) and how they use these tools.
- 🔄 Users can take steps like changing recovery email addresses or using VPNs to enhance their privacy, demonstrating personal responsibility in security.
- 🚫 Even within end-to-end encryption, users must be cautious about what they share, as digital sharing can lead to unintended consequences.
Q & A
What is the main concern raised by the media about Proton and Signal?
-The media claims that Proton and Signal are no longer secure platforms. Proton was reported to have complied with a request to hand over a recovery email address to Spanish police, and there are allegations that Signal is a front for the US government.
Why do some people react negatively to news about privacy companies cooperating with government requests?
-People often have a confirmation bias, believing that privacy and security are illusions. When they hear about privacy companies complying with government requests, they tend to dismiss the idea of privacy altogether without examining the details.
What is the legal framework that companies like Proton have to operate within?
-Companies must operate within the legal frameworks of their respective countries. If a government makes a legal, court-approved request for data, companies are required to comply, regardless of their privacy policies.
What limitations do companies have in terms of the data they can provide to authorities?
-Companies can only provide data that they actually have. Data that is end-to-end encrypted is useless to authorities without the encryption keys, which are held by the users themselves.
Why is it necessary for email sender and recipient information to be unencrypted?
-Sender and recipient information must be unencrypted for the email to be delivered. If this information were encrypted, the email could never be delivered, as it would not be recognizable by the email system.
What was Proton's response to the Spanish law enforcement request?
-Proton complied with the request from Swiss authorities to provide a recovery email address. However, they did not provide the user's name or any of their emails because they did not have that information.
What is the controversy surrounding Signal's encryption and its board of directors?
-There are claims that Signal's encryption has been exploited in US courts or media, and concerns about the chairman's history of promoting censorship and connections with the intelligence community. However, Signal is open source, and its code has been scrutinized by security researchers.
What is the primary message the speaker wants the audience to take away from the discussion?
-The speaker emphasizes that privacy apps and services are only as strong as the user who uses them. Users need to practice good operational security (OPSEC) and be responsible for their own privacy and security.
How can users enhance their operational security with Proton Mail?
-Users can remove or change their recovery email address in Proton Mail settings, use a burner email address, or turn off the allow recovery by email option. They can also use a VPN or TOR to hide their IP address when logging on.
What is the speaker's advice on sharing sensitive information within end-to-end encrypted platforms?
-The speaker advises caution, suggesting that the best way to keep information private is not to share it digitally in the first place. Users should be mindful of what they share, even within secure platforms.
Outlines

此内容仅限付费用户访问。 请升级后访问。
立即升级Mindmap

此内容仅限付费用户访问。 请升级后访问。
立即升级Keywords

此内容仅限付费用户访问。 请升级后访问。
立即升级Highlights

此内容仅限付费用户访问。 请升级后访问。
立即升级Transcripts

此内容仅限付费用户访问。 请升级后访问。
立即升级浏览更多相关视频
CompTIA Security+ Full Course: Security Controls & Frameworks
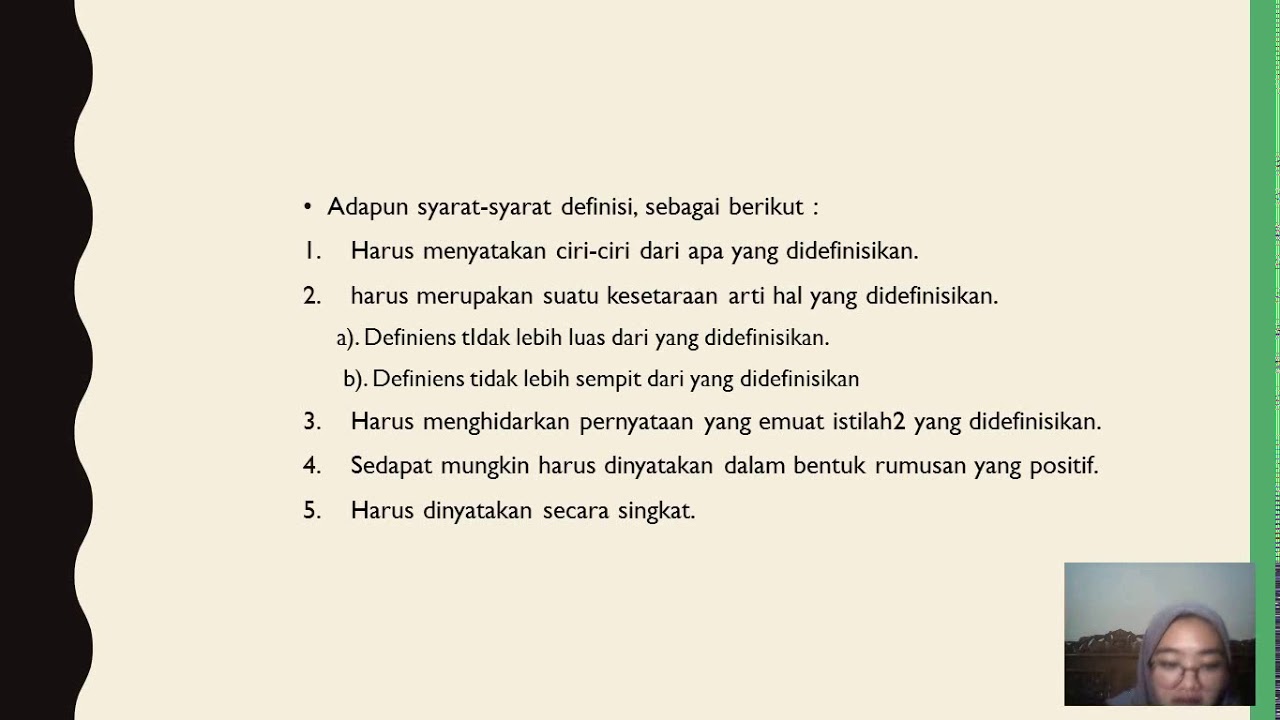
Definisi Pemerintahan & Tugas Pokok Pemerintahan

Aspek Legal TIK ~ Mata Pelajaran Informatika ~ Kelas XII

Cellphone Surveillance Explained - Stingray/IMSI Catchers

🔰NOVA LEI 14.967/2024- NOVO ESTATUTO DA SEGURANÇA PRIVADA🔰

Is the Future of Cyber Security jobs at Risk? (Tech Layoffs Surge!!)
5.0 / 5 (0 votes)
