Network Security
Summary
TLDRIn this lecture on computer network security, the focus is on tools like firewalls, VPNs, and IDS/IPS systems to protect networks from malicious activities. Firewalls regulate network traffic, ensuring only authorized access. VPNs create secure, encrypted tunnels for remote access, with various types for different needs (site-to-site, client-to-site, remote access, and mobile VPNs). IDS detects abnormal activity, while IPS goes further by actively blocking threats. These tools work together to safeguard both local and remote networks, ensuring that sensitive data remains secure from unauthorized access and cyber threats.
Takeaways
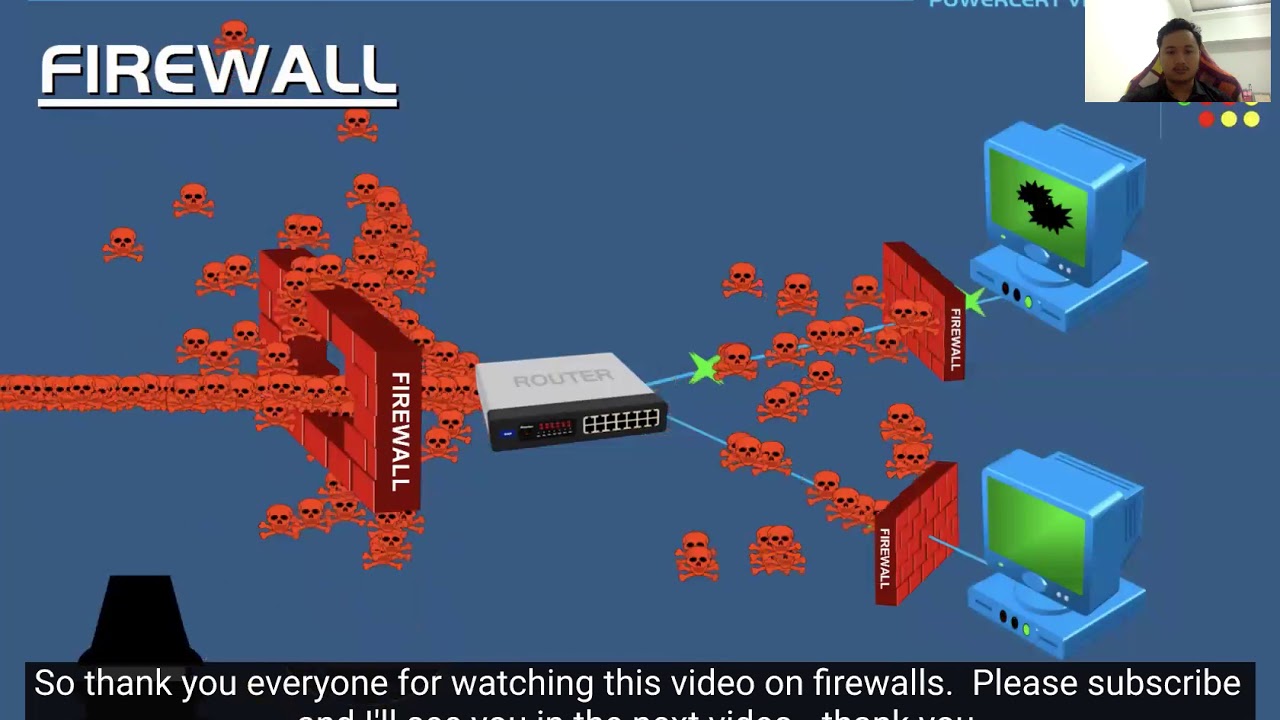
- 😀 Firewalls are essential for filtering network traffic and can be implemented as either hardware (network firewalls) or software (host firewalls).
- 😀 Network firewalls are placed near gateways to monitor traffic and enforce rules regarding which data can enter or leave the network.
- 😀 Host firewalls are typically part of antivirus software and focus on controlling traffic for individual devices.
- 😀 VPNs (Virtual Private Networks) create secure, encrypted tunnels to allow safe access to internal networks over the public internet.
- 😀 Site-to-site VPNs connect multiple locations, enabling secure communication between them over the internet.
- 😀 Client-to-site VPNs provide remote employees secure access to the company's internal network.
- 😀 Remote access VPNs are particularly useful for individuals working from home, allowing them to connect securely to company systems.
- 😀 Mobile VPNs are designed for users who need secure access while traveling or moving between different locations.
- 😀 VPN protocols such as PPTP, L2TP, OpenVPN, SSTP, and IKEv2 each offer different levels of security and functionality.
- 😀 IDS (Intrusion Detection Systems) monitor network traffic for suspicious activity and alert administrators to potential threats.
- 😀 IPS (Intrusion Prevention Systems) go a step further than IDS by actively blocking harmful traffic, providing a proactive security measure.
Q & A
What is the primary purpose of a firewall in computer networks?
-A firewall is used to filter network traffic, controlling which data packets are allowed or blocked based on rules set by a network administrator. It can filter traffic based on IP addresses, ports, and protocols.
What are the two main types of firewalls discussed in the script?
-The two main types of firewalls discussed are Network firewalls and Host firewalls. Network firewalls filter traffic between networks, while Host firewalls focus on filtering traffic specifically to and from individual devices.
How does a Network firewall differ from a Host firewall?
-A Network firewall is generally a hardware device that filters traffic on a network-wide scale, often placed near the gateway to monitor all incoming and outgoing traffic. A Host firewall, on the other hand, is usually a software application installed on individual devices, controlling traffic specific to that device.
What role does VPN play in securing network communications?
-A VPN (Virtual Private Network) creates an encrypted tunnel over the public internet, allowing secure access to private networks like an intranet. It prevents unauthorized entities from intercepting or snooping on sensitive data exchanged over the internet.
What is the difference between Site-to-Site VPN and Client-to-Site VPN?
-A Site-to-Site VPN connects two or more networks (like branch offices) securely over the internet, while a Client-to-Site VPN connects a remote user to a private network, typically using a username and password for authentication.
Why is OpenVPN commonly used?
-OpenVPN is widely used because it is open-source, flexible, and supports both UDP and TCP protocols. It uses SSL/TLS for encryption, making it secure, and is compatible with multiple operating systems.
What are the benefits of using L2TP over PPTP for VPN connections?
-L2TP (Layer 2 Tunneling Protocol) is generally considered more secure than PPTP (Point-to-Point Tunneling Protocol) as it can use digital certificates or pre-shared keys for authentication and runs on UDP, which is fast but less reliable than TCP. L2TP is often used for connections requiring more security.
How does SSL VPN (SSTP) differ from other VPN protocols like PPTP?
-SSTP (Secure Socket Tunneling Protocol) uses port 443, the same as HTTPS, which allows it to bypass firewalls that block other VPN ports. It is more secure and harder to block compared to PPTP, which uses older encryption methods.
What are the key differences between Intrusion Detection System (IDS) and Intrusion Prevention System (IPS)?
-An IDS detects suspicious network traffic and generates alerts to inform administrators. In contrast, an IPS not only detects suspicious traffic but also actively takes preventive measures such as blocking traffic, blocking IP addresses, or terminating user sessions.
How does the IPS (Intrusion Prevention System) enhance security over IDS (Intrusion Detection System)?
-While IDS only alerts administrators about suspicious activity, IPS actively takes action by blocking malicious traffic, IP addresses, or even terminating user sessions, making it a more proactive security measure compared to IDS.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video

CompTIA Security+ SY0-701 Course - 4.5 Modify Enterprise Capabilities to Enhance Security
Pengantar Keamanan Sistem Informasi - Firewall + IDS + IPS

KEAMANAN JARINGAN | 3.1.2 POTENSI ANCAMAN KEAMANAN JARINGAN - FASE F (SMK TJKT)

IDS vs IPS vs Firewall #networksecurity #firewall #IPS #IDS

3.6. IP Vulnerabilities and Threats

Protecting your network part I - IDS, IPS, Honeynet, DMZ, proxy
5.0 / 5 (0 votes)